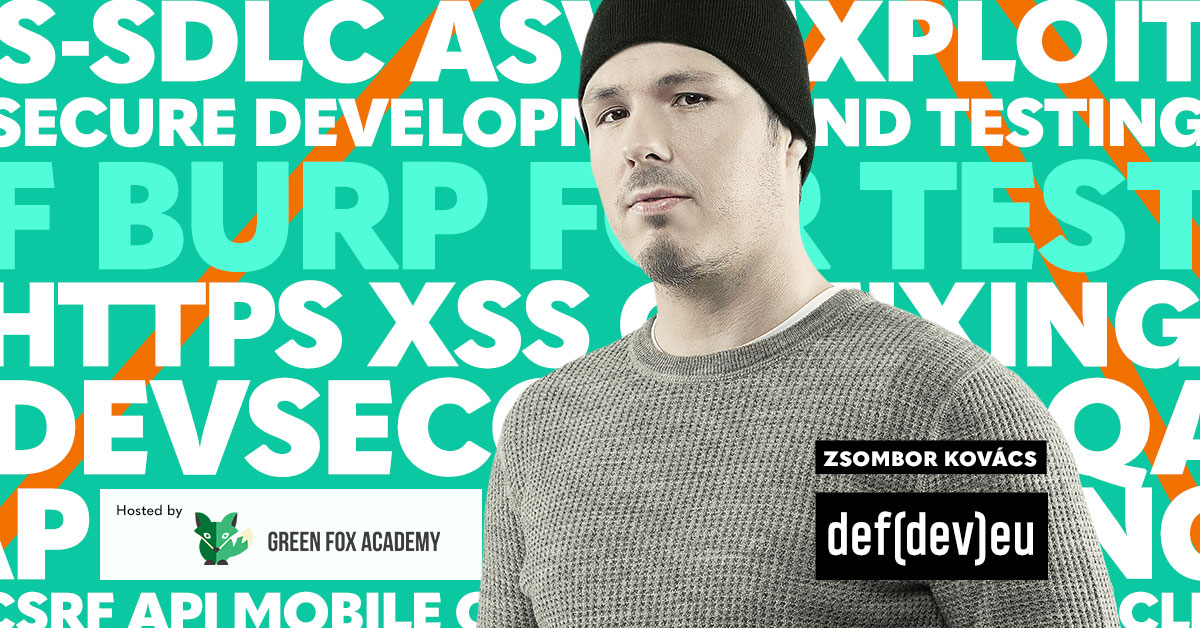
Zsombor Kovács is a security specialist with many years of hands-on experience in penetration testing in Budapest, London and Zürich. Besides penetration tests performed on mobile device (both iOS and Android) his main focus is application and infrastructure evaluation. Zsombor conducts penetration tests and malware analysis on a daily basis. He found vulnerabilities in all sorts of Android and iOS applications from e-banking and telecommunication to document management, to MDM. He also has been involved in projects dealing with incident response, forensic engineering, reversing, physical security and social engineering. Zsombor is keen on everything related to hacking from finding bugs in mobile applications to secdev consulting, to lock picking and RFID hacking and exploring the human psyche.
Recently, Zsombor got involved in secure development trainings on both mobile platforms.
From the trainings record of Zsombor:
LogMeIn, GoToMeeting, defdev1611, defdev1805